Secure and manage your evolving network with the industry-leading Network
Cisco Identity Services Engine
Secure and manage your evolving network with the industry-leading Network Access Control and Policy Enforcement platform
Cisco ISE provides Secure Network Access. It is the core of your Zero Trust approach for the Workplace. It delivers complete visibility by identifying, classifying, and assembling the necessary context on users and endpoints. It authenticates and authorizes them based on your business intent — your security policy –and grants an appropriate level of network access based on the limited needs of their roles or functions.
We provide expert assistance with developing implementation plans, installing, configuring, and integrating the new ISE solution or applications in your network.
Cisco Identity Services Engine (ISE) is an industry leading, Network Access Control and Policy Enforcement platform, that lets you,
See
Users, endpoints and applications
Secure
By controlling network access and segmentation
Share
Context with partners for enhanced operations
Leverage our experts knowledge for help with strategy and planning as well as design, implementation, and adoption. We collaborate with you to develop a customized implementation approach that determines your primary security goals.
We use this approach to understand how to design ISE so that it seamlessly integrates with your existing network design.
Our Advisory and Implementation Service also allows your network and security teams to closely align the ISE system with your overall security strategy and business objectives for increased ROI.
Cisco ISE Capabilities
Asset
Visibility
Guest and Secure
Wireless Access
Device
Administration
Secure Wired
Access
Segmentation
Security Ecosystem
Integrations
Threat
Containment
Device
Compliance
BYOD
Are you deploying a Cisco Identity Service Engine (ISE) solution?
Our Cisco ISE experts and product specialists are also available to help you explore how these benefits can address all of your security needs. Contact us We offer a comprehensive lifecycle of services, including Planning, Designing, Limited deployments/Proof of Concept, Mentored Installations, Upgrade process, technical and training services for the Cisco ISE solution

Maximize the Value of Cisco ISE with Integrated Solutions Cisco ISE and DNA enable SD-Access
Identity Services Engine
Network identity sensor and enforcer
Digital Network Architecture
Network design, policy, provisioning, and assurance
Software Defined Access (SDA)
SD-Access means business drivers define network intent and dictate the mechanics of network connectivity, not the other way around Built on the principles of Cisco’s Identity Services Engine (ISE) and Digital Network Architecture (DNA), Software Defined-Access (SD-Access) provides automated end-to-end segmentation to separate user, device and application traffic without redesigning the network. SD-Access automates user access policy so organizations can make sure the right policies are established for any user or device with any application across the network. This is accomplished with a single network fabric across LAN and WLAN. Pairing the two creates a consistent user experience anywhere without compromising on security.
SD-Access takes the complexity and the stress out of your growing network.
Cisco Stealthwatch
Scalable visibility and security analytics across your business
Most businesses invest heavily in their IT infrastructure and security, yet attacks get through and hostile internal actors operate with impunity. And am equally critical issue is that it takes months or even years to detect threats. This lack of threat visibility is a function of growing network complexity as well as constantly evolving attacks. And security teams, with their limited resources and disjointed tools, can only do so much. How do you know if your current security controls are working, managed, and configured properly? And how do you know these tools are doing the job that you need them to do?
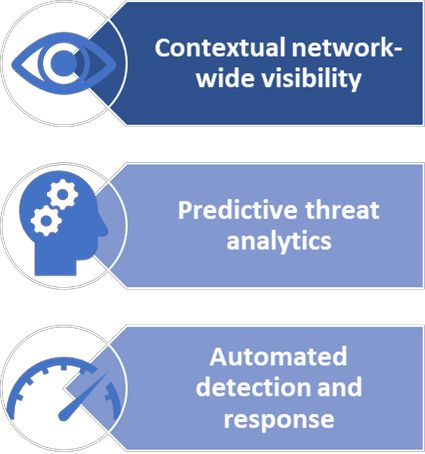
““Cisco Stealthwatch has helped us gain visibility into the internal traffic by 100% which has resulted in the identification of threats that were extremely difficult to detect previously.””
IT ArchitectLarge Enterprise Industrial manufacturing company
Protect your environment today.
Get in touch with us to see how Stealthwatch can secure your cloud deployments as well as your private network.